Artificial intelligence systems are now deeply embedded in modern life. They recommend what you buy, detect fraud, assist in medical diagnoses, and even help write software. Convenient, efficient, and occasionally…
Read More
Artificial intelligence is no longer a niche technology. It is embedded in everything from banking systems to healthcare diagnostics and marketing platforms. While AI brings efficiency and automation, it also…
Read More
Cyber threats used to be relatively predictable. A virus here, a phishing email there, maybe someone guessing “password123” and getting lucky. Those simpler times are gone. Today’s threats are faster,…
Read More
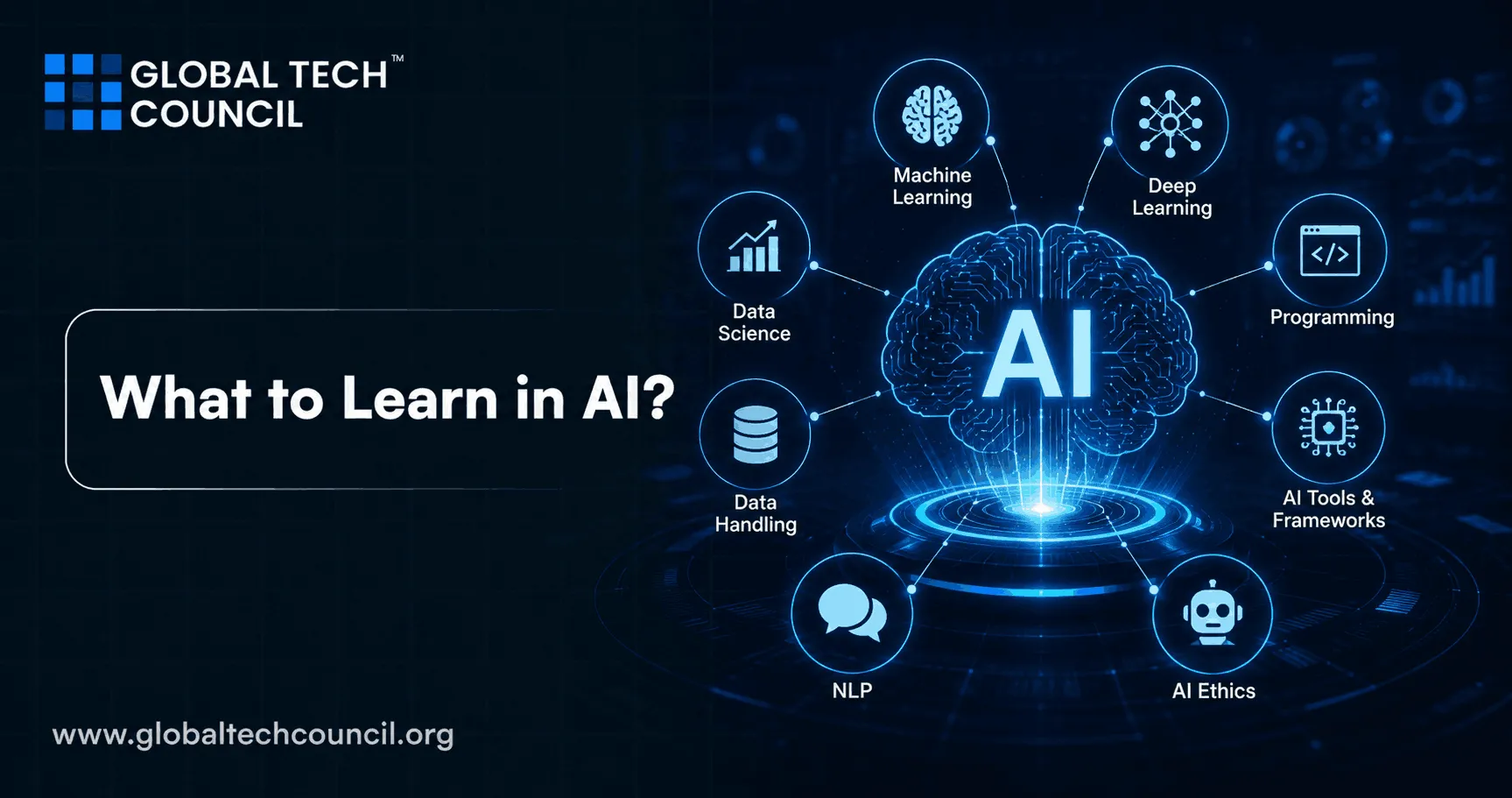
Machine learning has quietly become the engine behind modern technology. It powers recommendation systems, fraud detection, medical diagnostics, and even the tools used to write code itself. Convenient, efficient, and…
Read More
Cybersecurity used to rely heavily on static rules, manual monitoring, and a lot of crossed fingers. Then artificial intelligence showed up and quietly replaced “hope nothing breaks” with “we might…
Read More
Malware is any software designed to harm your computer, steal your information, or cause damage to your network. It can slow down your device, steal passwords, or even lock your…
Read More
If you want to protect your digital life, here’s the answer you’re looking for: follow these top 10 cybersecurity tips to keep your personal information, devices, and business safe. From…
Read More
Critical infrastructure security is the process of protecting the essential systems that keep our modern society running—like electricity, water, healthcare, finance, transportation, and communication. It involves defending these systems against…
Read More
Crossover Error Rate (CER) is an important concept in cybersecurity. It helps in measuring the accuracy of systems that identify users, such as fingerprint scanners and face recognition software. CER…
Read More
Cybersecurity is the procedure of defending individuals and companies from hackers attempting to gain accessibility to their networks with criminal intent. The proliferation of digital technologies, IoT, Cloud computing, and…
Read More