 Introduction
Introduction
Malware analysis is the process of examining malicious software to understand how it works, what it targets, and how to detect or contain it. Security teams use malware analysis to investigate incidents, improve defenses, support threat hunting, and produce indicators and rules that can stop future attacks.
This work has become more important as attackers scale operations and reuse tools quickly across campaigns. Microsoft’s Digital Defense Report 2025 highlights the speed and scale of modern cyber threats and notes broad AI adoption by both defenders and attackers, which increases pressure on security teams to analyze malware faster and more accurately.
In short, malware analysis is no longer just a specialist reverse engineering task for a few experts. It is a core operational function in modern security programs.
What Malware Analysis Does
Main Goals
Malware analysis helps answer practical questions during an incident:
- What does the malware do?
- How does it persist?
- What systems does it contact?
- What files, registry keys, or processes does it modify?
- How can we detect and block it?
CISA’s malware analysis services reflect this operational focus by providing dynamic analysis and recommendations that help organizations with removal and recovery actions.
Where It Fits in Security Operations
Malware analysis supports incident response, SOC investigations, threat intelligence, detection engineering, and vulnerability management. A single malware sample can produce artifacts used in SIEM detections, EDR blocklists, network signatures, and user awareness guidance.
That is why good analysis improves both immediate response and long-term resilience.
Core Malware Analysis Techniques
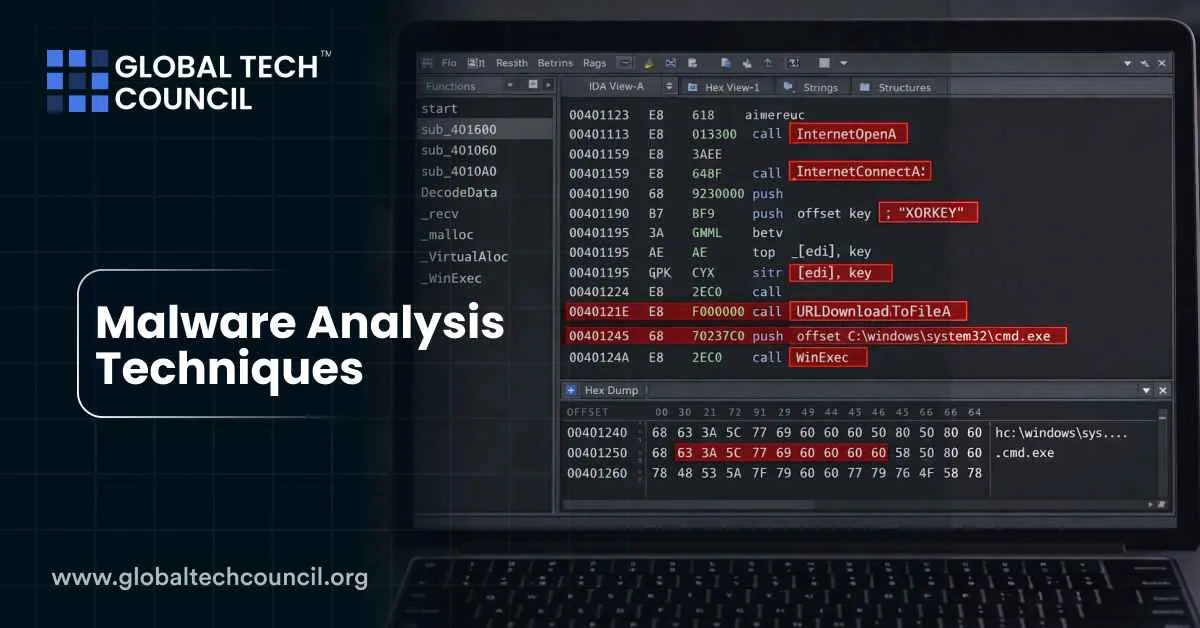
Static Analysis
Static analysis examines malware without running it. Analysts inspect the file structure, headers, strings, imports, metadata, and embedded resources to gather clues safely.
Common static checks include:
- File hashes and signatures
- PE or ELF header review
- Imported functions and libraries
- Suspicious strings (URLs, commands, registry paths)
- Packers or obfuscation indicators
Static analysis is often the first step because it is quick and reduces risk. It can reveal likely behavior before execution, such as credential theft functions, persistence mechanisms, or network communication libraries.
Dynamic Analysis
Dynamic analysis runs malware in a controlled environment to observe behavior. Analysts monitor processes, filesystem changes, registry edits, network connections, persistence attempts, and spawned commands.
This is where sandboxes and isolated virtual machines matter. CISA’s malware services and next-generation analysis support emphasize controlled environments for analysis, which reflects how central safe detonation has become in practical workflows.
Dynamic analysis is especially useful for malware that is heavily packed or obfuscated, where static analysis alone may hide the real payload.
Behavioral Analysis
Behavioral analysis focuses on what the malware does rather than just what code it contains. This includes tracking TTPs such as lateral movement attempts, credential dumping, persistence setup, scheduled tasks, or command-and-control (C2) communication patterns.
MITRE ATT&CK is widely used for this mapping because it provides a common language for techniques and adversary behavior. MITRE describes ATT&CK as a globally accessible knowledge base of adversary tactics and techniques based on real-world observations, and its October 2025 v18 release updated techniques, groups, campaigns, and software across domains.
This technique-based view helps teams write stronger detections than simple hash matching, which fails as soon as attackers recompile or repackage malware.
Reverse Engineering
Reverse engineering goes deeper into the malware code to understand logic, algorithms, evasion methods, and payload behavior. Analysts use disassemblers and decompilers to inspect functions, control flow, and API usage.
Reverse engineering is often necessary when:
- The malware is novel
- It uses custom encryption or obfuscation
- It includes anti-analysis checks
- Behavioral output is incomplete
- Defenders need durable detections
It is slower than basic static or dynamic analysis, but it provides the highest-quality understanding of how a sample operates.
Memory Analysis
Some malware hides behavior in memory, injects into legitimate processes, or uses fileless techniques. Memory analysis helps investigators capture running artifacts that may not be visible in the original file.
This can reveal decrypted payloads, injected code, command strings, and in-memory configurations. In incident response, memory analysis is often the difference between “we saw something suspicious” and “we know exactly what executed.”
Hybrid Analysis Workflows
In practice, teams rarely use one technique alone. They combine static inspection, sandbox execution, reverse engineering, and ATT&CK mapping in a layered workflow. The goal is not academic completeness but actionable outputs for detection and containment.
Because incidents happen on deadlines, not in ideal lab conditions.
Real-World Examples
Ransomware Investigation
A ransomware sample may be analyzed first with static techniques to identify packers, strings, and imports. Dynamic analysis then reveals file encryption behavior, dropped notes, and network callbacks. Reverse engineering may confirm encryption routines or key handling, while behavioral mapping links activity to ATT&CK techniques such as data encryption and defense evasion.
This layered process helps defenders create EDR detections, network indicators, and response playbooks quickly.
Developer-Targeting Malware
Recent malware targeting developers, such as updated macOS threats reported by Microsoft Threat Intelligence and covered widely in late 2025, shows why modern analysis must include persistence checks, browser data theft paths, and clipboard hijacking behavior in addition to basic signatures.
The takeaway is simple: malware analysis now often intersects with software supply chain, developer tooling, and credential theft risks, not just traditional endpoint infections.
Common Challenges
Evasion and Anti-Analysis
Modern malware often detects virtual machines, sandboxes, debuggers, or monitoring tools. It may delay execution, require user interaction, or hide payloads until certain conditions are met. This makes analysis slower and increases the need for customized environments.
Volume and Time Pressure
Security teams face too many samples and too little time. Microsoft’s reporting on threat scale illustrates the pressure defenders face daily, including millions of blocked malware attempts.
As a result, organizations need triage workflows to decide which samples deserve deep reverse engineering and which can be handled through automated classification and sandboxing.
Tooling and Skill Gaps
Malware analysis requires a mix of operating system knowledge, networking, programming, reverse engineering, and incident response judgment. Many teams have tools but not enough trained analysts to use them effectively.
Recent Developments in Malware Analysis
More Behavior-Focused Detection
One clear trend is the move toward behavior-based analysis and detection. As malware families mutate rapidly, defenders rely less on static indicators alone and more on process behavior, ATT&CK technique mapping, and multi-signal correlation. MITRE’s continuing ATT&CK updates support this approach by keeping technique and software mappings current.
Greater Use of Automated Analysis Pipelines
Organizations are expanding automated detonation, enrichment, and triage pipelines to handle sample volume. CISA’s malware analysis and next-generation analysis services also reflect this modernization trend toward scalable analysis support in controlled environments.
Automation speeds analysis, but it works best when paired with human review for high-risk or unusual samples.
AI Changes Both Offense and Defense
Recent threat reporting also points to AI increasing cyber threat complexity, which raises the bar for analysts. Microsoft’s 2025 reporting notes AI adoption by threat actors and defenders alike, reinforcing the need for faster, more adaptive malware analysis workflows.
Best Practices for Organizations
Use Layered Analysis
Start with static and dynamic triage, then escalate to reverse engineering and memory analysis when needed. This balances speed and depth.
Isolate Analysis Environments
Use controlled sandboxes and dedicated lab systems. Never analyze live malware on production devices. It should not need saying, but here we are.
Map Findings to ATT&CK
Translate raw malware behavior into ATT&CK techniques to improve threat hunting, detection engineering, and executive reporting.
Turn Analysis Into Action
Every analysis should produce outputs: indicators, YARA rules, Sigma detections, firewall blocks, EDR hunts, or incident response guidance.
Skills and Certifications
Malware analysis requires technical depth and clear communication. A Tech certification can strengthen broader IT, systems, and cybersecurity foundations relevant to analysis labs, networks, and security operations. A Cybersecurity certification can be useful as cybersecurity becomes increasingly important in threat analysis, prioritization, and detection workflows. A marketing certification and Deep Tech Certification may also help security professionals communicate threats, awareness guidance, and risk messages clearly to business teams and non-technical stakeholders.
Conclusion
Malware analysis techniques are essential for understanding and stopping modern cyber threats. Static analysis, dynamic analysis, behavioral mapping, reverse engineering, and memory analysis each provide different pieces of the puzzle. The most effective security teams combine these techniques in layered workflows that produce fast, actionable outputs for detection and response.
As attacker tooling evolves and threat volume increases, malware analysis is becoming more automated, more behavior-focused, and more tightly connected to threat intelligence and SOC operations. The malware keeps adapting, so defenders need analysis processes that adapt faster. A rude requirement, but a real one.
 Introduction
Introduction